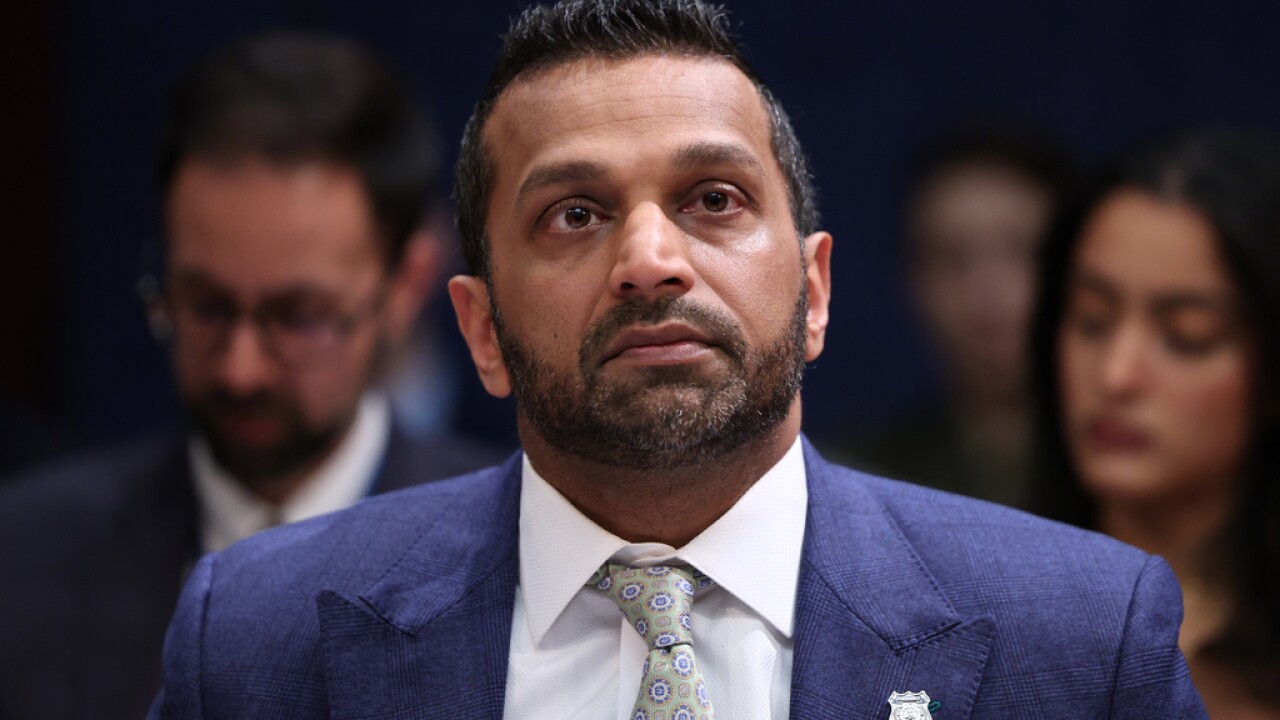
WASHINGTON — A brazen cyberattack targeting the personal email account of Kash Patel has sent shockwaves through the U.S. national security community, as officials confirm that hackers linked to the Iranian government accessed and publicly released private materials belonging to the nation’s top law enforcement official. The incident, which emerged within the past 24 hours, is being described by analysts as one of the most significant and symbolically damaging cyber intrusions involving a senior U.S. official in recent years, unfolding against the backdrop of escalating geopolitical tensions between Washington and Tehran.
According to multiple reports, the breach was carried out by a group calling itself the “Handala Hack Team,” a cyber collective widely believed by Western intelligence experts to be affiliated with Iranian state-backed cyber operations. The group claimed responsibility for infiltrating Patel’s personal Gmail account and subsequently posted a cache of emails, photographs, and documents online. U.S. officials have confirmed that the account was indeed compromised and that at least some of the materials released appear to be authentic.
The disclosure immediately raised alarms not only because of the target—who leads the Federal Bureau of Investigation—but also because of the broader implications for cybersecurity vulnerabilities at the highest levels of government. While early assessments suggest the exposed materials were largely personal in nature and dated back several years, the symbolic impact of the breach has intensified scrutiny of how foreign adversaries are targeting American officials in an increasingly aggressive cyber landscape.
The hackers published a range of content they claimed to have extracted from Patel’s account, including personal photographs showing the FBI director in private settings, along with documents such as a résumé and correspondence spanning roughly a decade. Some of the materials, according to reporting, date from between 2010 and 2019 and include both personal and limited professional communications.
In a statement relayed through reporting, a Justice Department official confirmed the breach and said the materials circulating online appeared to be genuine, though authorities emphasized that no classified or sensitive government information had been compromised. The FBI itself has not issued a detailed public statement as of this writing, but officials have indicated that steps were taken to mitigate any potential risks associated with the exposure.
Even so, cybersecurity experts caution that the distinction between “personal” and “official” information is not always clear-cut, particularly when it comes to high-ranking government officials. Personal accounts can often contain contacts, contextual information, or fragments of communication that, when aggregated, may provide valuable intelligence to adversaries.
The Handala group, which claimed responsibility for the attack, framed the breach as part of a broader campaign against U.S. interests. In messages posted alongside the leaked materials, the group taunted Patel and criticized American cybersecurity defenses, suggesting that the attack was both a retaliatory measure and a demonstration of capability.
The timing of the breach is particularly notable. It comes amid heightened tensions involving Iran, Israel, and the United States, as well as a recent U.S. law enforcement crackdown on cyber networks linked to Iranian intelligence. Just days before the incident, the Justice Department reportedly moved to seize several internet domains associated with groups believed to be connected to Iranian cyber operations—a move that analysts say may have provoked retaliatory action.
In that context, the attack on Patel appears less like an isolated incident and more like part of a broader pattern of cyber escalation. Iran has long been accused of using proxy groups and loosely affiliated hacker collectives to conduct cyber operations, allowing it to maintain plausible deniability while still advancing its strategic objectives. This approach, often described as “hybrid warfare,” blends elements of state-sponsored activity with the tactics of decentralized cyber actors.
Experts note that groups like Handala are particularly difficult to attribute definitively, as they operate in the gray area between independent hacktivism and direct state control. However, Western intelligence agencies have repeatedly linked similar groups to Iran’s Ministry of Intelligence and Security, suggesting that their activities are at least tacitly supported, if not directly coordinated, by the Iranian government.
The breach also underscores the evolving nature of cyber warfare, where the goal is often not to steal secrets in the traditional sense but to create disruption, embarrassment, and psychological impact. By targeting a figure as prominent as the FBI director, the attackers achieved a high-profile demonstration of reach and capability, sending a message not only to U.S. officials but also to domestic and international audiences.
“This is as much about perception as it is about data,” one cybersecurity analyst said in response to the incident. “When you can show that you’ve penetrated the personal communications of someone at that level, it raises questions about what else might be vulnerable.”
Those questions are now being asked across Washington, where lawmakers and security officials are seeking to understand how the breach occurred and what it reveals about broader vulnerabilities. While details remain limited, early indications suggest that the compromised account was a personal email address rather than a government-issued system, highlighting the persistent challenge of securing non-official communication channels.
The use of personal accounts by government officials has long been a point of concern within the national security community. While such accounts may offer convenience, they often lack the robust security measures applied to official systems, making them attractive targets for foreign intelligence services. In recent years, multiple incidents involving hacked personal accounts have prompted calls for stricter guidelines and oversight.
In this case, the fact that the compromised materials appear to be historical in nature may limit the immediate operational impact. However, experts warn that even older data can be valuable, particularly when it comes to building profiles of individuals, mapping networks of contacts, or identifying potential avenues for future exploitation.
The incident also raises broader questions about the resilience of U.S. cyber defenses at a time when digital threats are becoming increasingly sophisticated. Over the past decade, Iran has significantly expanded its cyber capabilities, developing a range of offensive tools and techniques that have been used to target both government and private-sector entities.
Recent attacks attributed to Iranian-linked groups have included disruptions to critical infrastructure, corporate data breaches, and influence operations aimed at shaping public opinion. The targeting of Patel’s email account represents a continuation of that trend, with a focus on high-value symbolic targets.
At the same time, the breach comes amid internal challenges within U.S. law enforcement and intelligence agencies. Recent reporting has highlighted concerns about staffing, resources, and institutional capacity, particularly in the face of growing cyber threats. Some analysts worry that these challenges could exacerbate vulnerabilities, making it more difficult to detect and respond to sophisticated attacks.
For the Biden—now Trump—administration, the incident presents both a security challenge and a political test. Officials must balance the need to respond decisively to the breach with the risk of escalating tensions further, particularly in an already volatile geopolitical environment. While no specific retaliatory measures have been announced, the attack is likely to factor into ongoing discussions about U.S. cyber strategy and deterrence.
Meanwhile, the public release of Patel’s personal materials has sparked debate about privacy, ethics, and the role of cyber operations in modern conflict. While the hackers framed their actions as a form of political resistance, critics argue that the exposure of personal information crosses a line, raising concerns about the normalization of such tactics.
For Patel himself, the incident adds to a tenure already marked by controversy and scrutiny. Since assuming the role of FBI director in 2025, he has faced criticism over a range of issues, from internal agency decisions to public conduct. Kash Patel The email breach, while not directly related to those matters, places him once again at the center of a high-profile national security story.
As investigators work to assess the full scope of the breach, several key questions remain unanswered. It is not yet clear how the hackers gained access to Patel’s account, whether additional data remains undisclosed, or whether other officials may have been targeted as part of the same campaign. The answers to those questions could have significant implications for both immediate security measures and longer-term policy decisions.
What is clear is that the incident represents a stark reminder of the vulnerabilities inherent in an increasingly interconnected world. Even as governments invest heavily in cybersecurity, the human element—personal accounts, individual behaviors, and the complexities of digital communication—continues to present opportunities for adversaries.
In the coming days and weeks, the breach is likely to remain a focal point of both media coverage and policy debate, serving as a case study in the challenges of defending against modern cyber threats. For the United States, the episode underscores the need for vigilance, adaptation, and a clear understanding of the evolving tactics employed by foreign adversaries.
For now, the hack of the FBI director’s personal email stands as both a warning and a signal—a warning of the risks posed by sophisticated cyber actors, and a signal that the digital front lines of geopolitical conflict are as active and consequential as ever.